The rise of the internet and innovations in information technology have certainly made the lives of healthcare professionals and patients easier. However, this change has also come with challenges in protecting data from different types of cyber attacks. Let’s review the most common types of cyber attacks in healthcare and how to recognize them.
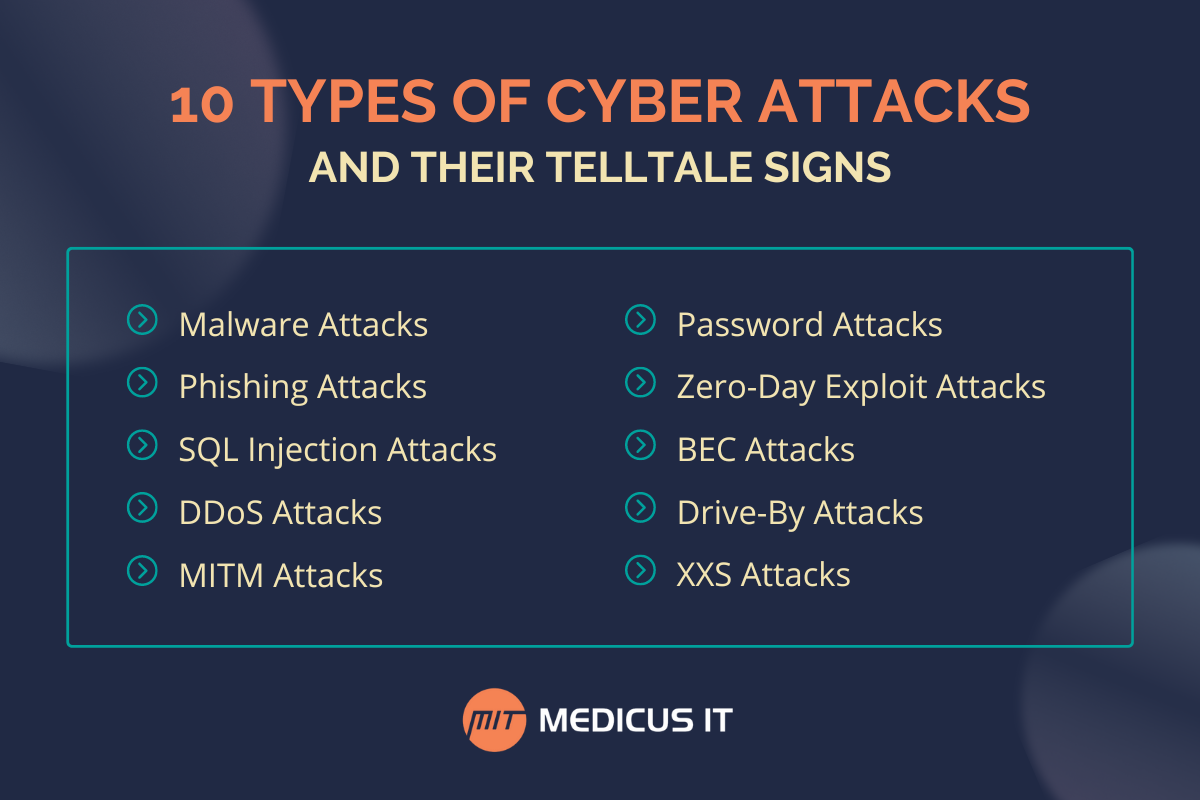
10 Types of Cyber Attacks
Cybercrime has become more threatening than ever — especially in healthcare. It’s important to be aware of the types of attacks that can put your organization, providers, and patients at risk.
Malware Attacks
The term malware encompasses all malicious software viruses, such as worms, ransomware, spyware, and more. This software is installed without user consent to destroy data, spy on activity, or affect system functionality.
Phishing Attacks
Phishing is one of the most common types of cyber attacks in healthcare and includes sending malicious mass emails disguised as being from a trusted source. By clicking on the links in these emails, users grant attackers access to their system and invite them to download malicious software, steal data, and more.
SQL Injection Attacks
Structure Query Language (SQL) attacks occur on database-driven websites and involve injecting malicious code into the search box to reveal sensitive data. This allows hackers to edit, delete, and in some cases, gain administrative rights to data.
DDoS Attacks
Distributed Denial of Service (DDoS) attacks occur when hackers flood systems, servers, and networks with an overwhelming amount of traffic beyond the supportable bandwidth. By shutting the entire system down, DDoS attacks create a vulnerable environment for other types of cyber security attacks to enter the network.
MITM Attacks
Also known as an eavesdropping attack, Man-In-The-Middle (MITM) attacks involve an attacker intercepting communication between two parties to steal financial information, sensitive personal information, credentials, and more. MITM attacks commonly occur on public Wi-Fi, making them one of the most difficult to detect of all types of attacks in cyber security.
Password Attacks
This attack involves hackers entering a system by cracking a user’s password. This is accomplished using various methods, such as a Brute Force attack, Dictionary attack, Password Spraying, and more.
Zero-day Exploit Attacks
This attack occurs when hackers learn about an existing vulnerability in widely used software. The hackers intentionally attack organizations that utilize the software to easily gain access to data.
BEC Attacks
On our list of types of cyber attacks, Business Email Compromise (BEC) attacks can be one of the most financially destructive. This occurs when an attacker targets a specific member of the organization by email. They carefully research information about the organization and pretend to be a fellow team member to convince the employee to send funds.
Drive-by Attacks
Drive-by Download attacks are commonly used to spread malware by enticing the victim to visit a malicious website that infects their device. Unlike other common types of cyber attacks in healthcare, the user doesn’t have to actively permit this attack by downloading malicious files or opening an email for it to occur.
XXS Attacks
A Cross-site Scripting (XXS) attack occurs when hackers inject malicious scripts into the code of a trusted website. These attacks are often initiated by sending a malicious link to users, which affects their system with malware when they click on it.
Telltale Signs of Cyber Attacks
The most common types of cyber attacks continue to challenge the healthcare industry and threaten the security of patient data. Unusual activity in your healthcare organization’s database is a telltale sign of a cyber attack. Unusual activity can include:
- Slow network speeds. Slower-than-normal network operation is one of the first signs of a cyber attack. Hackers could use a high volume of network resources to initiate an attack.
- Phishing issues. A large number of phishing emails is a sign your organization is becoming the prime target of a cyber attack.
- Suspicious software. If your staff is experiencing an annoying amount of pop-ups, crashes, browser redirection, etc., you could be the target of malware.
- Locked accounts. Passwords may have been compromised if you notice staff members are locked out of accounts or applications can’t be accessed.
- Unfamiliar Programs. Unrecognizable programs running in the task manager or activity monitor may be malicious software downloaded without consent.
Get Protected From New Types of Cyber Attacks
It’s important to understand the types of cyber attacks and how to prevent them. Where patient safety is a concern, IT security shouldn’t be taken lightly. Having a suite of preventative security procedures in place ensures patient data is secure. Frequent network scans, organization-wide security testing and planning, and day-to-day cybersecurity management are crucial components of protection against new types of cyber attacks in healthcare.
A cybersecurity provider who understands the complexity of healthcare IT is necessary to protect patient data and sensitive information. Medicus IT believes in preventative care for IT, focusing on the systems and solutions designed to protect your medical practice’s data. From auditing and compliance to day-to-day security management, Medicus understands healthcare IT and is prepared to advance your organization’s technology infrastructure. With essentials like risk assessment, incident response, security enforcement, and monitoring, Medicus’ cybersecurity services help keep your practice out of harm’s way. Contact us today to learn more about how the experts at Medicus can help protect your practice.